Grab your coffee. Here are this week’s highlights.
📅 Today’s Picks
dotenvx: Commit .env Files to Git Without Leaking Secrets
Problem
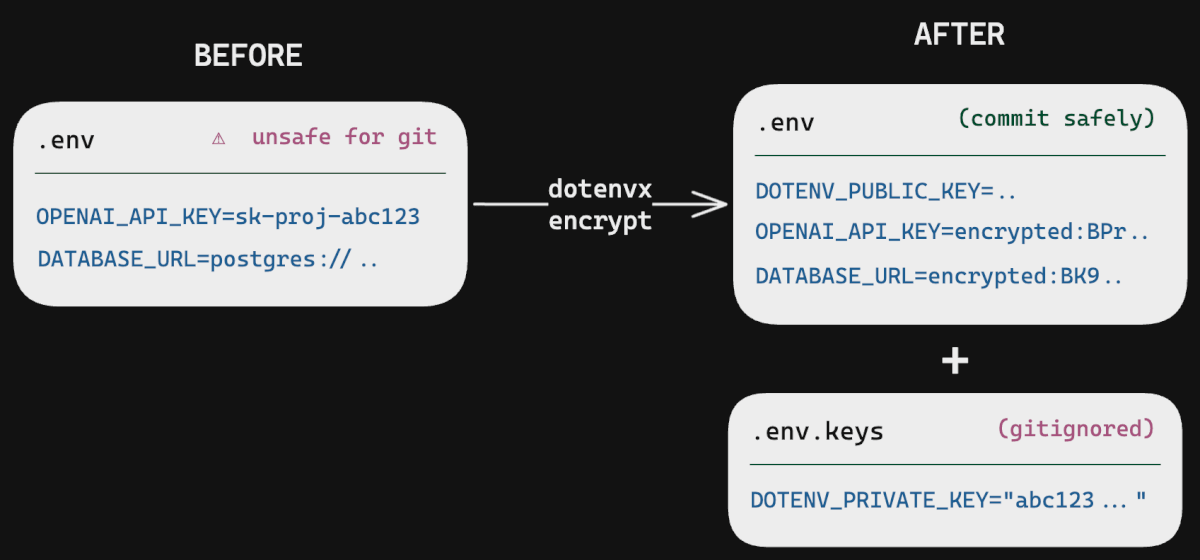
A .env file stores configuration like API keys and database URLs in plain text.
Because of that, committing it to git would leak every secret. Teams usually gitignore the file and distribute credentials manually through Slack or password managers instead.
Over time, this leads to secrets being scattered across different places without a clear source of truth.
Solution
dotenvx changes this by encrypting .env files with public-key cryptography.
You can commit the encrypted file to git, and your team only needs a private key (kept in a gitignored .env.keys file) to decrypt it when running the application.
Key capabilities:
- Works with Python, Node, Go, Ruby, Rust, and more via a single CLI
- Encrypts
.envfiles using the same cryptography as Bitcoin (secp256k1) - Separates environments with
.env.production,.env.staging, and.env.ci - Requires zero infrastructure (no Vault, no KMS, no cloud setup)
Bandit: Find Python Security Flaws with One Pre-Commit Hook
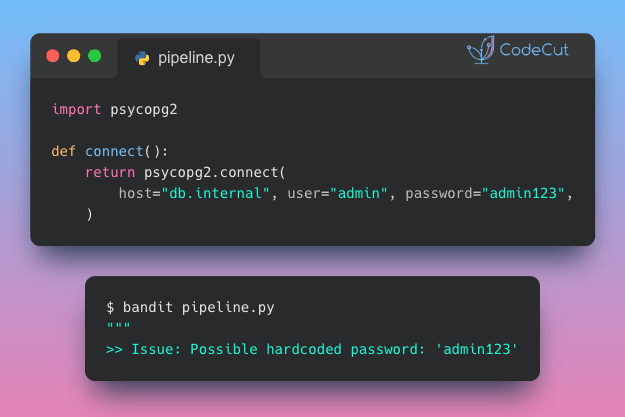
Problem
AI code generators can produce working code in seconds, but they often introduce risky patterns like hardcoding passwords or API keys directly in the source.
These issues can easily slip through a quick review.
Solution
Bandit is a Python security linter that automatically detects vulnerability patterns in your code, from hardcoded secrets to unsafe function calls.
Key capabilities:
- Detects hardcoded passwords, tokens, and API keys
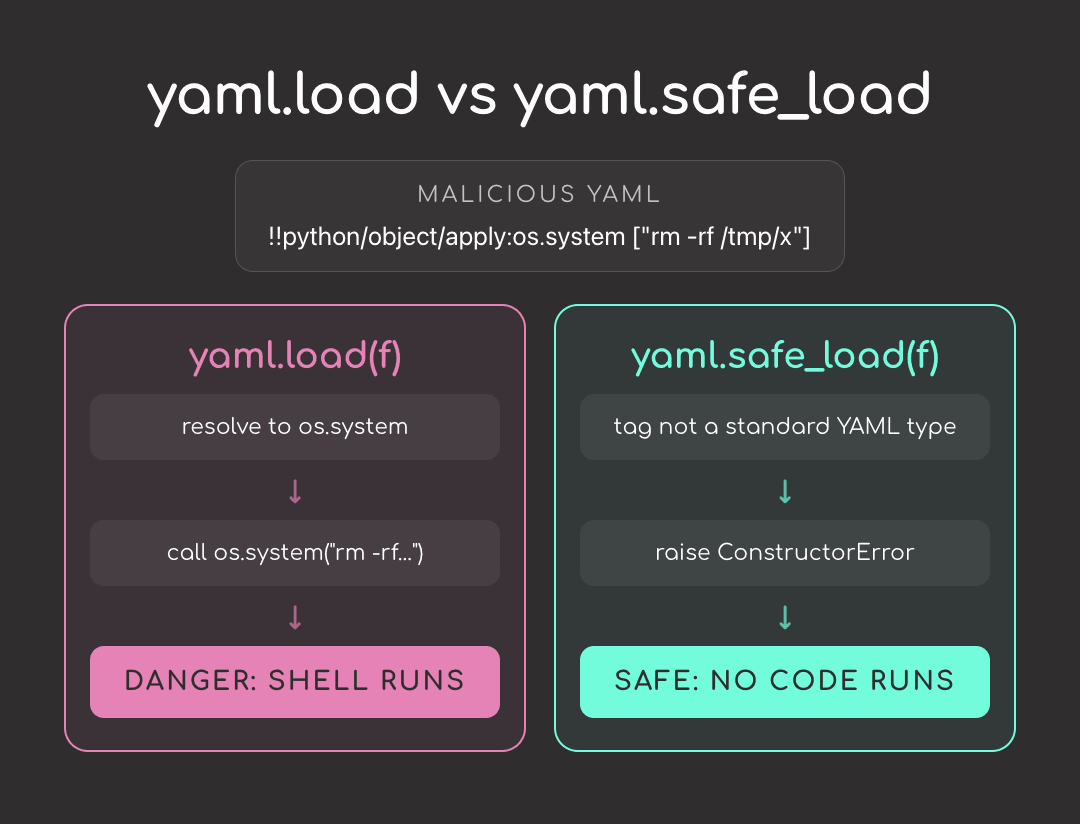
- Flags risky calls like
eval,exec, andpickle - Seamlessly integrates into pre-commit hooks, CI workflows, and editors
- Generates severity-ranked reports so you can prioritize fixes
☕️ Weekly Finds
vulture [Code Quality] – Find dead Python code with confidence-scored static analysis
responses [Testing] – A utility library for mocking out the Python Requests library
beartype [Code Quality] – Unbearably fast near-real-time pure-Python runtime type-checker
Looking for a specific tool? Explore 70+ Python tools →
Stay Current with CodeCut
Actionable Python tips, curated for busy data pros. Skim in under 2 minutes, three times a week.